Adam Tanner and Andy Greenberg are both Forbes contributers. Greenberg says of himself, “Covering the worlds of data security, privacy and hacker culture.” He covers much of the political controversy of personal data sales on his feed. Tanner says about himself, “I write about the business of personal data.” His Forbes feed features a wide variety of articles about how the companies, governments, and individuals around you are or could be using your personal data. In many cases, these are likely uses you do not want.
After reading many of their articles, I thought some of their reports too surprising not to re-post.
United States Postal Service: Selling Your Change of Address
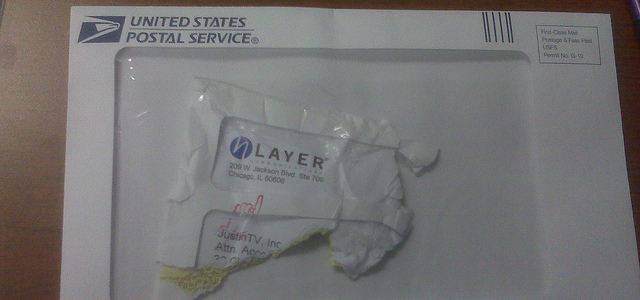
Many people are already quite fed up with the bad job of the United States Postal Service. The price of stamps is always increasing and yet the quality seems to constantly decrease. The picture above is of “delivered mail.” Despite the fact that the sender paid the same as everyone else to deliver that letter, it looks like it’s only 20% of what the sender put in his mailbox actually made it. That’s the Postal Service for you.
However, perhaps their inadequacy goes a step further, when updating your address with them actually produces more junk mail than real. In “How The Post Office Sells Your New Address To Anyone Who Pays (And The Little-Known Loophole To Opt Out)“, Tanner reports that the Postal Service is actually the one to blame for the junk mail you receive at your new house. He writes:
It’s all there in the fine print when you sign up for a change of address: “We do not disclose your personal information to anyone, except in accordance with the Privacy Act.” Then it lists a number of exceptions including “to mailers, if already in possession of your name and old mailing address, as an address correction service.”
… “Either weekly or monthly we distribute an updated file of change-of-address data to the licensed companies,” Betts said. “Mailers submit their address lists directly to these commercial data processors who update the information and return to the mailer.”
… If you want to forward your mail, the USPS does not offer an option to opt out of sharing the data, or even paying for the privilege of opting out. Members of Congress have from time to time proposed creating an opt-out option, but to date such initiatives have failed. Some continue to lobby for the idea.
…”USPS justifies the program on the grounds that they don’t ‘sell’ the list but license its use. That is a subterfuge. Supposedly, you only get a new address if you have the old address already. Because data brokers have every household in America in their files, the information goes from NCOA to the data brokers, who flag every change and resell lists of new movers to anyone.”
There is, however, a loophole that keeps data brokers from accessing your updated address. When you fill out the online form to change an address, you can indicate a temporary change that provides six months of forwarding that can then be extended for another six months. That information, unlike the changes marked as permanent, is not included in the master list sold to data brokers.
Even if you do not file a change of address with the post office, data brokers often learn that you have moved when you update your magazine subscriptions, deed registrations, phone connections, credit card details or have transitions with other companies. Then they include you into a list of ‘new movers.’ Data brokers such as Experian sell such lists to doctors and dentists, lawn maintenance services, furniture and appliance dealers and others who want to lure the business of the new kid in town.
Perhaps if this were two private companies it wouldn’t feel like such an egregious breach of privacy. You don’t need update your address with FedEx or UPS, for example.
We would expect a government agency to handle our personal information with more care than to just sell it to any company who wants to subscribe. On the eve of universal healthcare, such disregard for privacy is just appalling.
Your Web Camera: Taking Your Picture

Do you know what you do in front of your computer? Someone else might. In “Two-Year-Old Flash Bug Still Allows Webcam Spying On Chrome Users,” Greenberg says:
One stray click to look at an image or video online, and the web could start watching you back.
On Thursday Russian security consultant Egor Homakov published a proof-of-concept exploit that allows anyone to hide a script inside a clickable image that can surreptitiously activate any Google’s Chrome user’s webcam and photograph them. According to Homakov, the sneaky webcam spying trick, first discovered by another Russian hacker, uses a bug in Flash of which Adobe has been aware for two years. But that bug apparently still hasn’t been fixed, at least for users of Google’s browser.
… Update: Adobe spokesperson Heather Adell points me towards this update from Google, which says the bug is now fixed. “I want to emphasize this bug resided in Google Chrome, not Flash Player,” she writes.
Although the bug has now been fixed, all it takes is another computer error, careless programmer, or maliciously intended individual to potentially make the error come back again. Furthermore, the error itself was granting permission for the internet to gain access to your web camera without explicitly asking for it. However, many times when it does ask for permission, internet users grant it anyways. This is not a bug but rather a self-created potential leak of your image.
The same permissions error (or self-created leak) can happen with any aspect of your computer, including your microphone.
The one simple fix, according to Greenberg? “A Post-It over the camera.” No pictures can be taken when you’ve essentially put a lens cap on.
As for the other things you might accidentally leak to the internet, always make it a policy to click “Deny” when things ask for Internet access, unless you really trust them.
Your Browser Settings: Identifying Your Internet Presence

Many people concerned about internet privacy have cookies disabled on their computer. A sneaky way of at least identifying one computer’s set of users, cookies can track all sorts of personal internet usage. However, as Tanner notes in “The Web Cookie Is Dying. Here’s The Creepier Technology That Comes Next,” there may be something worse replacing it.
Many Internet advertisers rely on cookies, digital code stored on your browser. Some websites place multiple cookies when you visit, allowing them to track some of your activity over time (you can see who is tracking you by installing an application such as Ghostery or Abine’s “DoNotTrackMe”).
The problem for marketers is that some users set their browsers to reject cookies or quickly extinguish them. And mobile phones, which are taking an increasing chunk of the Web usage, do not use cookies.
To combat the cookie’s flaws, advertisers and publishers are increasingly turning to something called fingerprinting. This technique allows a web site to look at the characteristics of a computer such as what plugins and software you have installed, the size of the screen, the time zone, fonts and other features of any particular machine. These form a unique signature just like random skin patterns on a finger. The Electronic Frontier Foundation has found that 94% of browsers that use Flash or Java – which enable key features in Internet browsing – had unique identities.
… One business transparent about such efforts is a San Francisco start up called AdStack. They have developed a technology that allows firms to send an email but deliver the content only when a user opens it, giving the sender a chance to change the message in a few milliseconds. The email is sort of like a picture frame, with the content delivered interactively much as a webpage. They aim to deliver a personalized message at the right time.
This new method of tracking differs from cookies in that you can’t ever choose to opt out. With cookies, at least you can always choose to simply delete them, clean out the data they’ve collected and make them start fresh. With fingerprinting, although it is conceivable you could chance precisely the right feature to change your fingerprint, that change could be at the cost of valued functionality.
Department Stores: Finding You From Your Zip Code And Credit Card

Many times, we trust that people in uniform have our best interests at heart. Too often, we are sadly mistaken. At Forbes in an article titled “Never Give Stores Your ZIP Code. Here’s Why“, Adam Tanner reveals that stores which ask for your zip code are really acquiring your address and targeting you with ads. He writes:
How does this work? In one of their brochures, direct marketing services company Harte-Hanks describes the GeoCapture service they offer retail businesses as follows: “Users simply capture name from the credit card swipe and request a customer’s ZIP code during the transaction. GeoCapture matches the collected information to a comprehensive consumer database to return an address.” In a promotional brochure, they claim accuracy rates as high as 100%.
Fair Isaac Corp., a company best known for its FICO credit scores, also offers a similar service which they say can boost direct marketing efforts by as much as 400%. “FICO Contact Builder helps you overcome the common challenges of gathering contact information from shoppers—such as complicating or jeopardizing the sales process by asking for an address or phone number, or complying with regulations,” it says. “It requires minimal customer information captured at point-of-sale, just customer name or telephone number and the customer or store ZIP code.”
Think about it. You live in a zip code with perhaps five significant figures worth of people. Have you ever met someone with your full name? Chances are you’re the only one.
An even more astounding fact is that apparently zip code, date of birth, and gender is the clincher. With those three pieces of information, you can find almost anyone. Tanner in “Harvard Professor Re-Identifies Anonymous Volunteers In DNA Study” reports:
Of the 1,130 volunteers Sweeney and her team reviewed, about 579 provided zip code, date of birth and gender, the three key pieces of information she needs to identify anonymous people combined with information from voter rolls or other public records. Of these, Sweeney succeeded in naming 241, or 42% of the total. The Personal Genome Project confirmed that 97% of the names matched those in its database if nicknames and first name variations were included. She describes her findings here.
Sweeney has also set up a web page for anyone to test how unique their birthdate, gender and zip are in combination. When I tried it, I was the only match in my zip code, suggesting that I, like so many others, would be easy to re-identify. “This allows us to show the vulnerabilities and to show that they can be identified by name,” she said. “Vulnerabilities exist but there are solutions too.”
… Sweeney’s latest findings build on a 1997 study she did that showed she could identify up to 87% of the U.S. population with just zip code, birthdate and gender.
The website for testing revealed that sometimes a precise birthday is not even necessary. Simply having the birth year or even a range of potential birth years could be sufficient for identification if your zip code’s population is small enough.
The United States Government: Tracking Social Groups Via Meta Data

The National Security Administration has gotten a lot of attention recently, since the leak that they’ve been monitoring most of our phone usage as well as our electronic lives.
Some people think this encroachment on our privacy is not big deal. They respond with a “I’ve got nothing to hide” or “Let it all out there” attitude. However, Malte Spitz wrote for The New York Times an opinion piece titled “Germans Loved Obama. Now We Don’t Trust Him.” He points out that with millions of meta data sets, “You could easily draw maps, tracing communication and movement. You could see which individuals, families or groups were communicating with one another. You could identify any social group and determine its major actors.”
Suddenly, it’s not your personal information you’re letting “all out there,” it’s the information of your friends, family, and organizations that you’re sacrificing. Although you may have nothing you’d like kept to yourself, perhaps your uncle dealing with a secret intellectual disability or your close friend who has just gotten pregnant does.
However, Tanner at Forbes points out:
It may raise hackles to think that U.S. intelligence officials might be monitoring your telephone and Internet communications, but for most of us it’s only the marketers who are really interested in our everyday online activities. And with many billions of dollars at stake, companies are increasingly turning to more sophisticated techniques to identify potential clients and deliver relevant advertising.
If government privacy violations upset you, marketing ones should upset you just as much. It’s not just famous people who have stalkers and it’s not just spies who have secrets they’d rather keep to themselves.
Conclusion
Obama has said, “You can’t have 100% Security and 100% Privacy.” That sentence should be revised. You cannot have 100% security. Period. End of thought. 100% security is impossible. Neither Obama nor anyone else can make you safe in this world.
However, on the topic of privacy, it would be funny (if it weren’t so sad) that our government so flippantly disregards our right to privacy (in lieu of pursuing the aforementioned unattainable security) while charging anyone who lifts the veil of their secrecy with espionage and forcing them to leave the country (mainly Edward Snowden).
Mark Hendrickson (yet another Forbes contributer) wrote in “Big Brother Is Increasingly Watching You“:
Increasingly, it feels like Big Brother is always watching and privacy is going the way of the dodo.
The government equivalent of individual privacy is secrecy. The difference is that individual privacy protects freedom, while government secrecy jeopardizes it. One of the great protections for a freedom-loving people is government transparency—the ability of citizens to keep a watchful eye on their elected representatives.
Unfortunately, as individual privacy has been declining in America, government secrecy has been increasing.
…Clearly, the balance between individual privacy and government secrecy is enormously out of whack. Individual privacy continues to shrink, while government secrecy continues to grow.
It was once wisely said (although not by Jefferson, to whom the quote is frequently misattributed), “When governments fear the people, there is liberty. When the people fear the government, there is tyranny.” We will fear the government less and be freer if we can recover our privacy and remove the veil of secrecy from government.
I don’t know about you, but I’m feeling more and more afraid.
Wondering what you can do to Support the Right to Privacy of Correspondence?
Photo, photo, photo, photo, and photo used here under Flickr Creative Commons.
3 Responses
Grayson @ Debt Roundup
I would say that this is scary, but I have known about these little tricks for years. These holes are in every privacy policy and this is the price we pay for wanting so many deals and savings. The retailers and companies know what they are doing.
Megan Russell
What is interesting to me is that in the case of department stores and junk mail, the only way they can find you and your address is by means of the government. It’s from public records or from USPS licenses that they acquire your information.
I didn’t get a chance to agree to a privacy policy statement with the government. Anyone with a bit of information on someone and Internet access is privy (via government websites) to the home address of that individual. What a disservice to U.S. citizens.
In the words of a close friend, “Regular people have stalkers too.”
Megan Russell
Should have added this one to the list as well:
The United States Police Force: Tracking Your Car
As reported by Anne Flaherty at Yahoo!News:
Jim Harper at CATO Institute also adds: